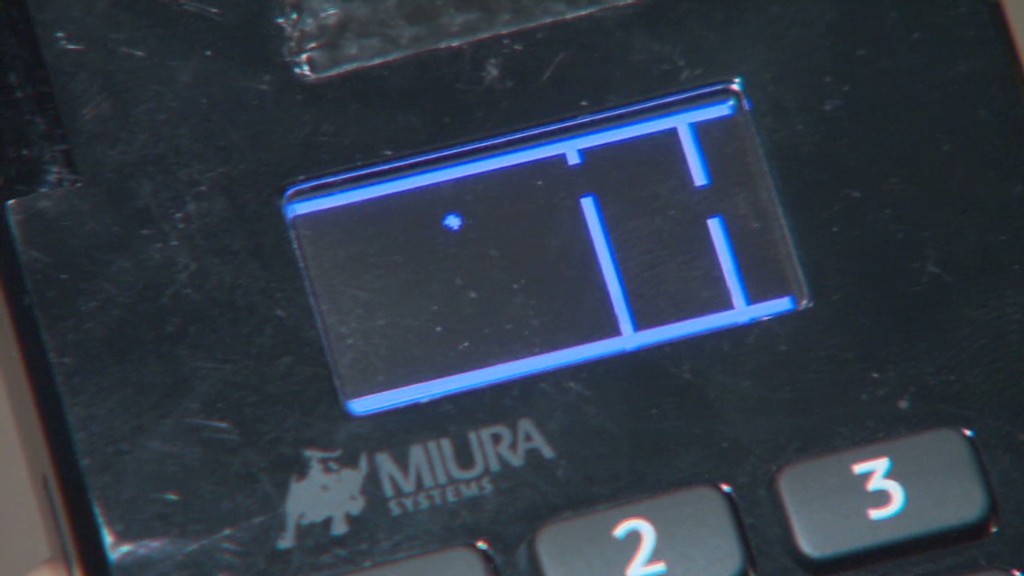
Get ready for a facepalm: 90% of credit rating card readers at this time use the similar password.
The passcode, set by default on credit rating card machines given that 1990, is easily discovered with a swift Google searach and has been exposed for so prolonged there is certainly no sense in hoping to disguise it. It really is possibly 166816 or Z66816, dependent on the machine.
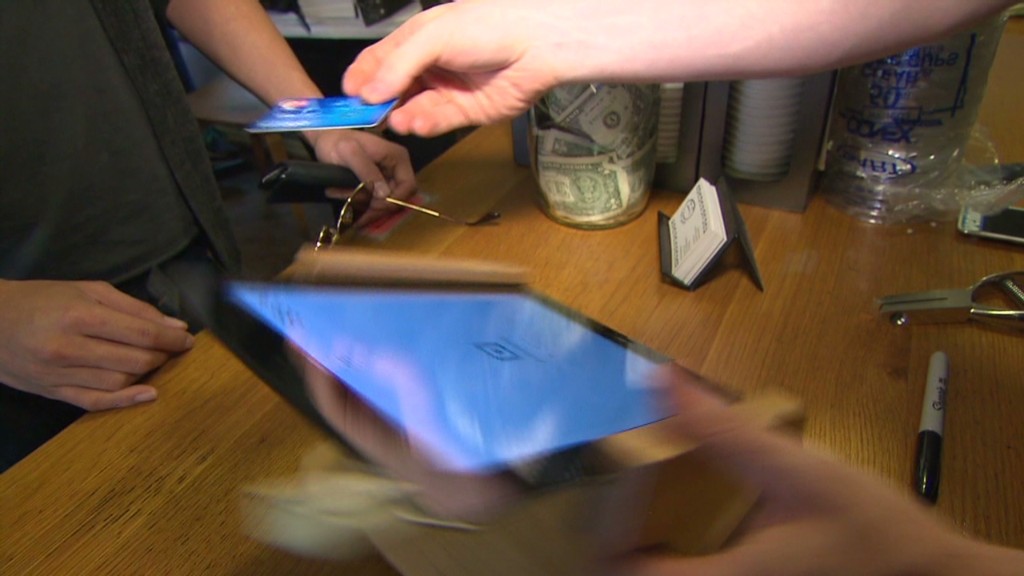
With that, an attacker can acquire complete control of a store’s credit history card audience, possibly allowing for them to hack into the devices and steal customers’ payment knowledge (assume the Focus on (TGT) and Household Depot (Hd) hacks all above again). No question big stores maintain shedding your credit score card information to hackers. Stability is a joke.
This most recent discovery comes from researchers at Trustwave, a cybersecurity company.
Administrative entry can be used to infect devices with malware that steals credit history card details, described Trustwave executive Charles Henderson. He comprehensive his conclusions at final week’s RSA cybersecurity meeting in San Francisco at a presentation known as “That Issue of Sale is a PoS.”
Just take this CNN quiz — discover out what hackers know about you
The challenge stems from a recreation of incredibly hot potato. Machine makers market devices to distinctive distributors. These sellers promote them to suppliers. But no a single thinks it can be their task to update the grasp code, Henderson informed CNNMoney.
“No a person is altering the password when they set this up for the 1st time everybody thinks the security of their level-of-sale is somebody else’s duty,” Henderson explained. “We are producing it fairly quick for criminals.”
Trustwave examined the credit score card terminals at a lot more than 120 retailers nationwide. That includes significant clothes and electronics outlets, as effectively as community retail chains. No precise suppliers have been named.
The large the vast majority of equipment ended up built by Verifone (Shell out). But the identical concern is present for all significant terminal makers, Trustwave stated.

A spokesman for Verifone reported that a password by itself is not ample to infect machines with malware. The corporation said, right up until now, it “has not witnessed any assaults on the protection of its terminals centered on default passwords.”
Just in circumstance, though, Verifone stated shops are “strongly suggested to change the default password.” And presently, new Verifone equipment occur with a password that expires.
In any circumstance, the fault lies with vendors and their exclusive sellers. It is like residence Wi-Fi. If you purchase a home Wi-Fi router, it is up to you to modify the default passcode. Suppliers really should be securing their have machines. And machine resellers must be helping them do it.
Trustwave, which helps defend stores from hackers, claimed that maintaining credit rating card equipment risk-free is very low on a store’s checklist of priorities.
“Organizations invest extra money deciding on the color of the stage-of-sale than securing it,” Henderson said.
This difficulty reinforces the summary produced in a recent Verizon cybersecurity report: that shops get hacked for the reason that they’re lazy.
The default password matter is a critical situation. Retail personal computer networks get exposed to laptop or computer viruses all the time. Look at just one case Henderson investigated not too long ago. A unpleasant keystroke-logging spy computer software ended up on the computer system a keep uses to course of action credit card transactions. It turns out staff members experienced rigged it to engage in a pirated version of Guitar Hero, and accidentally downloaded the malware.
“It exhibits you the degree of access that a great deal of persons have to the point-of-sale surroundings,” he stated. “Frankly, it truly is not as locked down as it ought to be.”
CNNMoney (San Francisco) Initially posted April 29, 2015: 9:07 AM ET






More Stories
Web Browser Based Call Accounting Software
Branches of Accounting, Uses of Accounting and Limitations of Financial Accounting
Here’s Why Every Business Needs An Accounting Team